Hello/Salut/Hoi/Hallo,
If you landed here, then you probably want to learn a bit about the person behind it.
Let me try and make a nice introduction then.
I’m Mihai, a Customer Solutions Architect, former Network/Systems/Security/whatever falls upon my hands engineer, a techie person always eager to learn more and expand his knowledge.
Wait, wait…what does this really mean ?
I am a deep dive techie that wanted to also learn a bit about how a company and the sales process works so I reoriented myself toward a more mixed role (technical PreSales and its various names across the industry spectrum).
Tech side experience
I work on a daily basis with various Clouds (AWS, Azure, GCP, OCI, Alibaba) and went through the whole spectrum of technologies like Linux (lately also a bit of eBPF), FreeBSD/OpenBSD, Solaris, Cisco (6500, 7600, ASR9K, Nexus, UCS), Juniper (MX, QFX, Contrail), Security (Linux based firewalls, ASA, SRX, penetration testing / trying out vulnerabilities in API of services or exploits and patching accordingly), Virtualization (VMWare, KVM) and Containers (Docker, Kubernetes, Openshift).
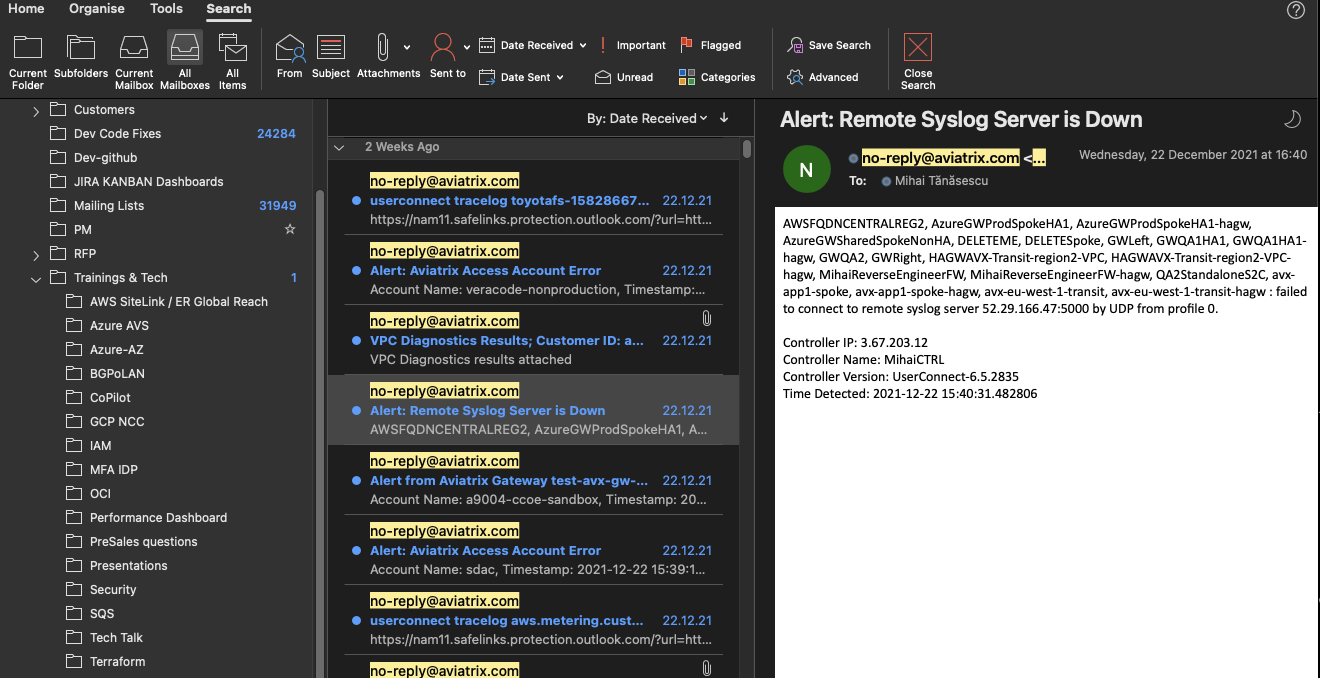
I’m also fascinated with seeing how a blackbox solution works (this means breaking into it, seeing how it’s built, tracing its logic and most fun…finding where programmers cut corners in implementation as a consequence of strict timelines and sales push).
Despite being able to read code, reverse engineer it, change it or adapt it to my needs I don’t see myself as a programmer, albeit ChatGPT & Bard make programming seem easy nowadays. => Intent based programming
Hobbies
- Hiking
- Badminton
- Cooking, albeit sometimes it ends up with smoke signals
- Travelling to non-touristic places, learning about the culture, customs, traditions around the world
(still wanting to reach Buthan at some point in my life)
Self improvement courses
- Financial Education / Passive income course + coaching
- NLP (Neuro-linguistic Programing) course + bootcamp
- Public Speaking course
Languages I speak
- Romanian and sometimes being a grammar freak
- English
- German
- French
- Italian
Books I’ve read
- Hoi, your Swiss German survival guide (Sergio J. Lievano, Nicole Egger) :)
- How to Stop Worrying and Start Living (Dale Carnegie)
- Amp it UP (Frank Slootman)
- From Strength to Strength (Arthur C. Brooks)
- The Subtle Art of Not Giving a F*ck (Mark Manson)
- The 7 Habits of Highly Effective People (Stephen R. Covey)
- Crossing the Chasm (Geoffrey A. Moore)
- Launch (Jeff Walker)
- The Wisdom of Insecurity (Alan Watts)
- The Qualified Sales Leader (John McMahon)
- Yes!: 50 Scientifically Proven Ways to Be Persuasive (Noah Goldstein’s, Steve Martin’s and Robert Cialdini)
- Influence Science and Practice (Tom Peters)
- Negotiation Genius (Deepak Malhotra, Max Bazerman)
- How to Win Friends and Influence People (Dale Carnegie)
- Why we sleep (Matthew Walker)
- The Warren Buffett Way (Robert Hagstrom)
What will basically be around here?
Anything in the lines of:
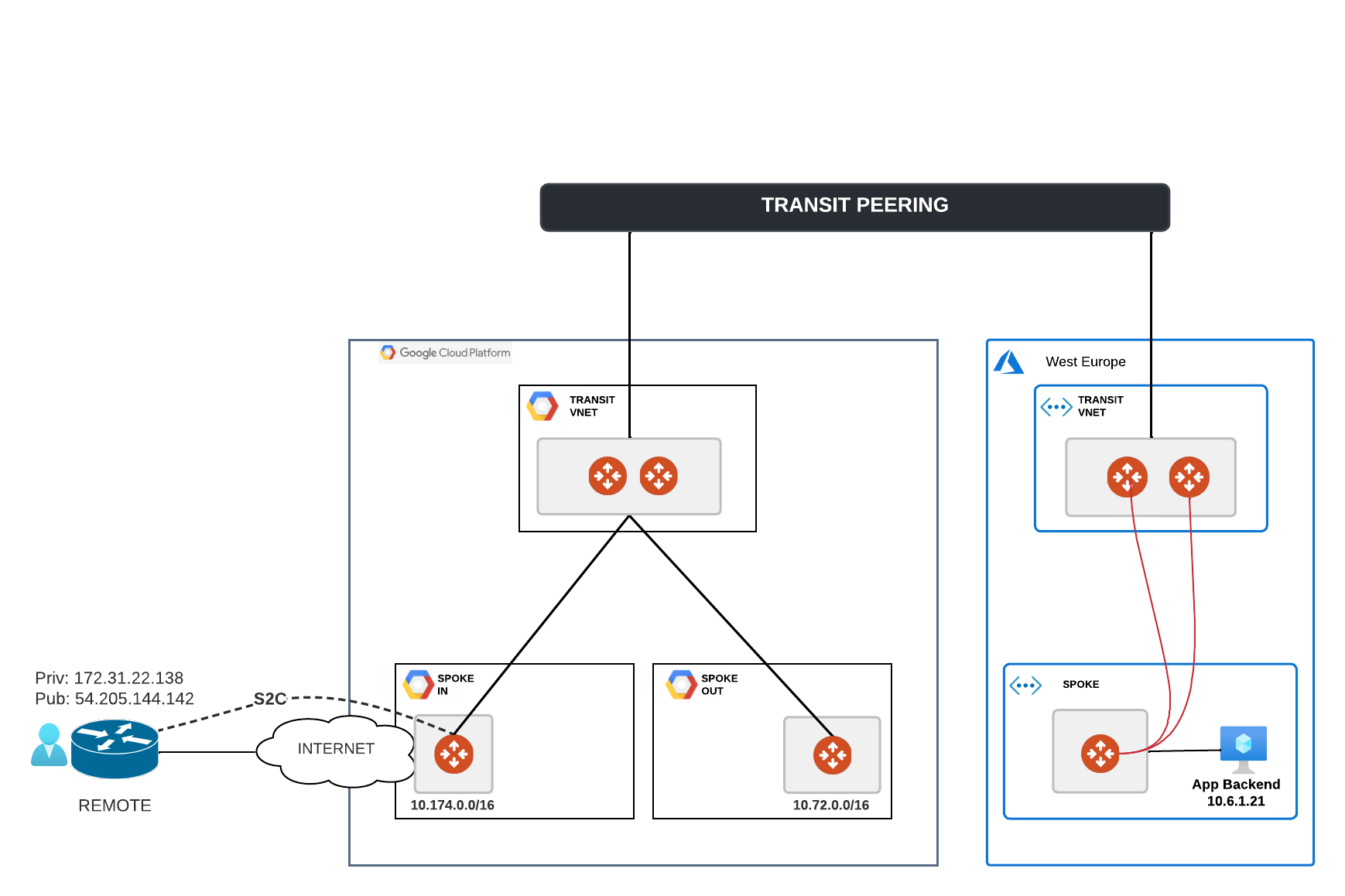
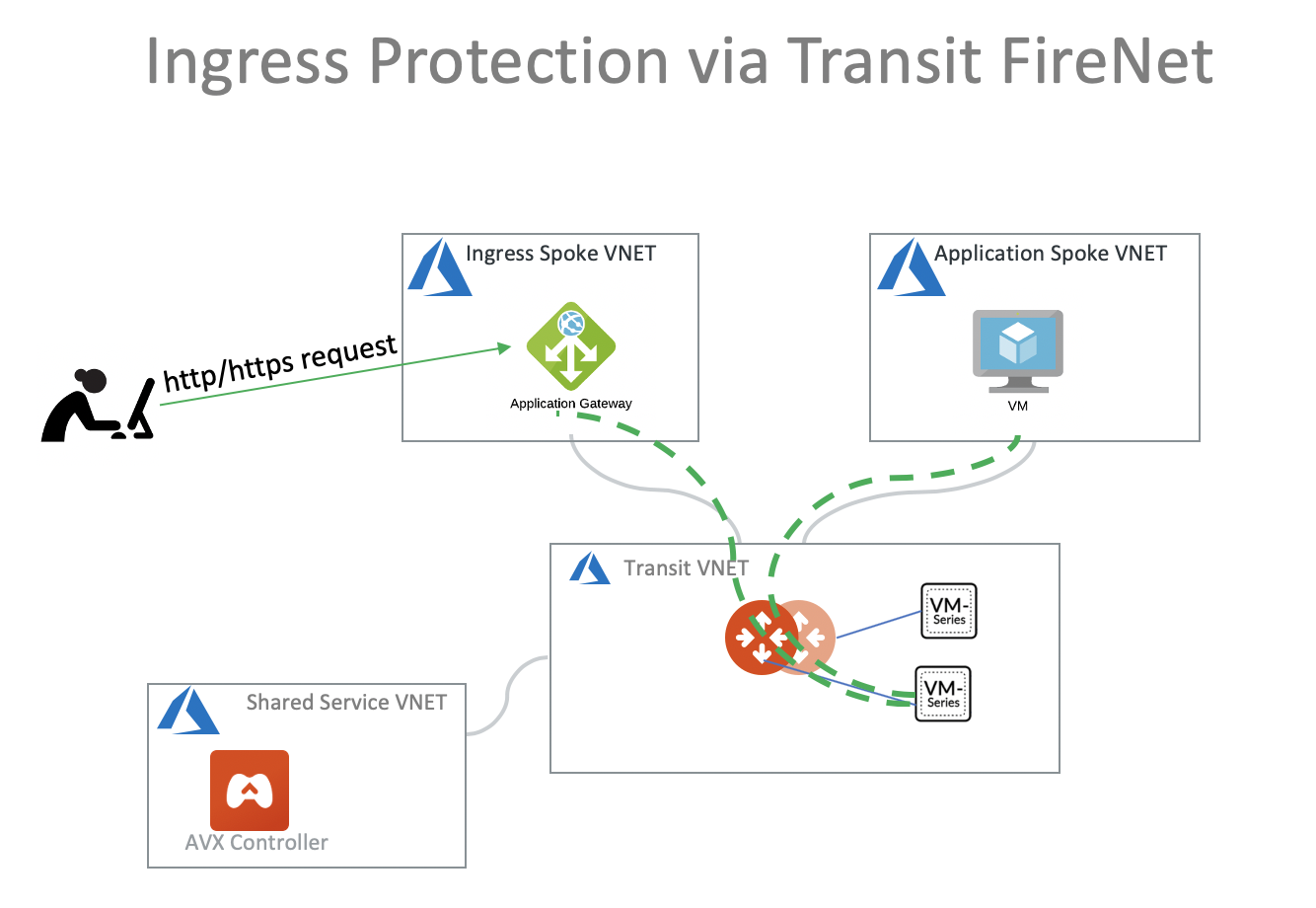
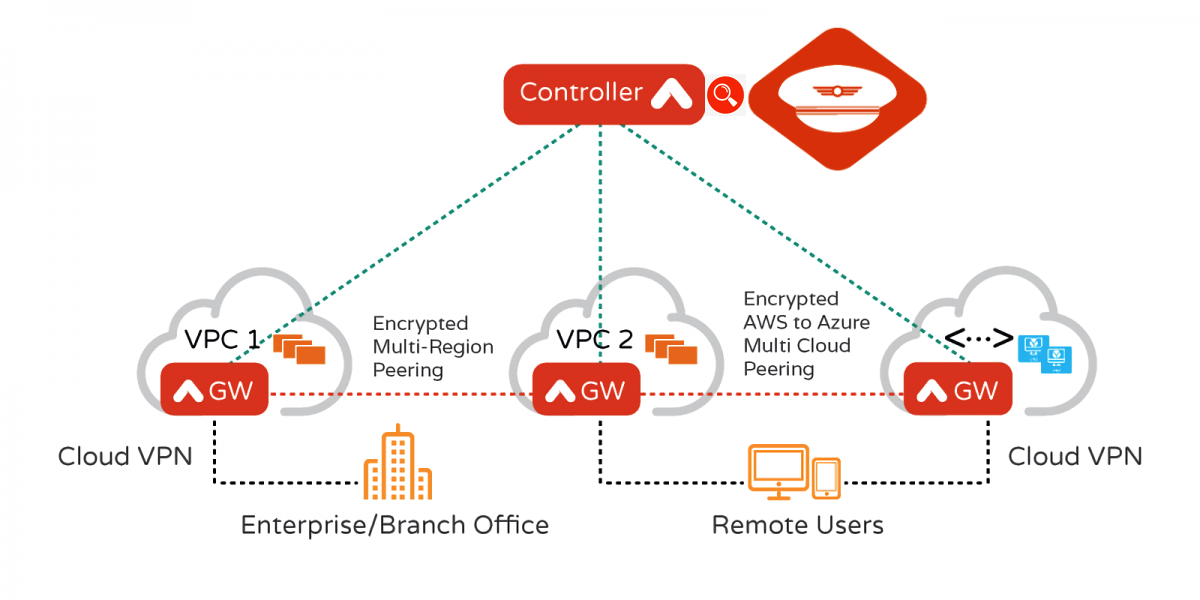
- Cloud/MultiCloud
- Network / Systems Engineering
- Openshift / Openstack / virtualization / datacenter topics
- Security (after some sleepless nights I passed the Offensive Security OSCE)
- Reverse engineering products, solutions, Linux stuff
- Other topics (I did my own Romanian automated Sour Cabbage solution using a pump, a Raspberry PI, a Relay Board and Home Assistant)
Continue reading